Solutions
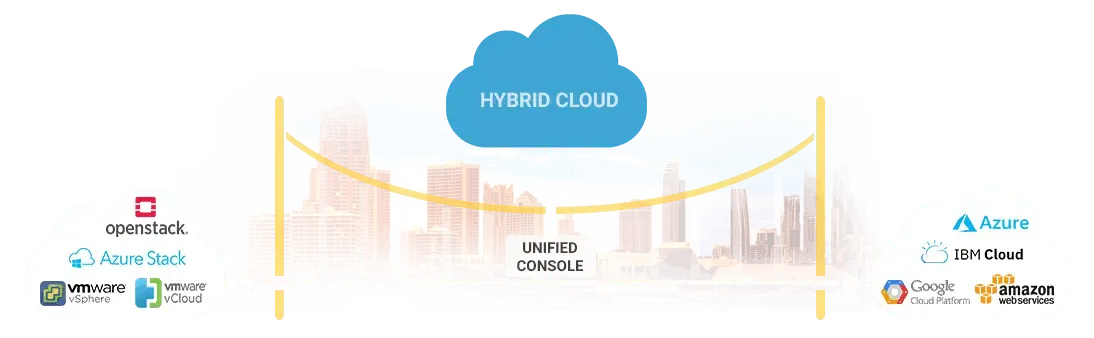
One-stop destination to procure, discover, manage and bill a wide array of cloud-based and non-cloud services, applications, and resources.
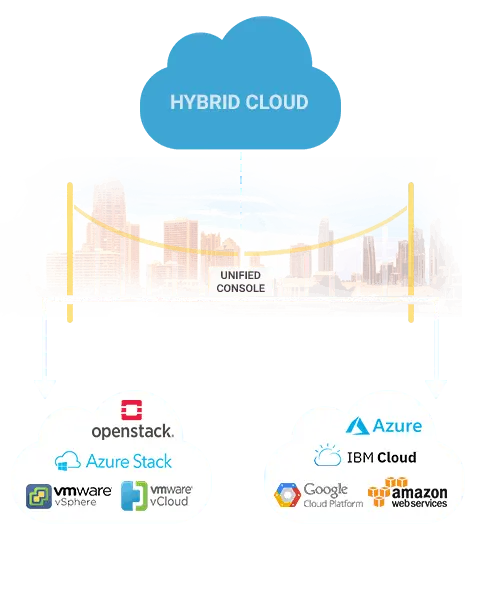
Empower your organization to transform its business and IT operations models by deploying a Cloud Service Broker solution.
Discover a hassle free way of selling SD-WAN Solutions for Service Provider's using Jamcracker's Digital Marketplace.
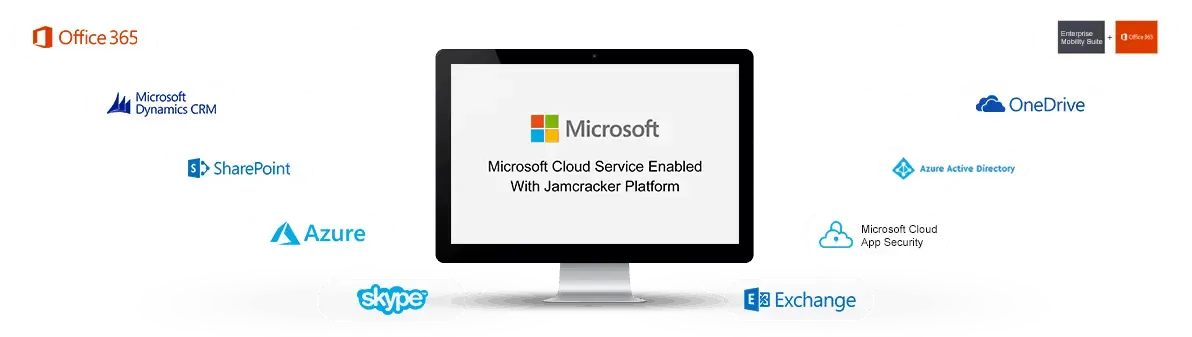
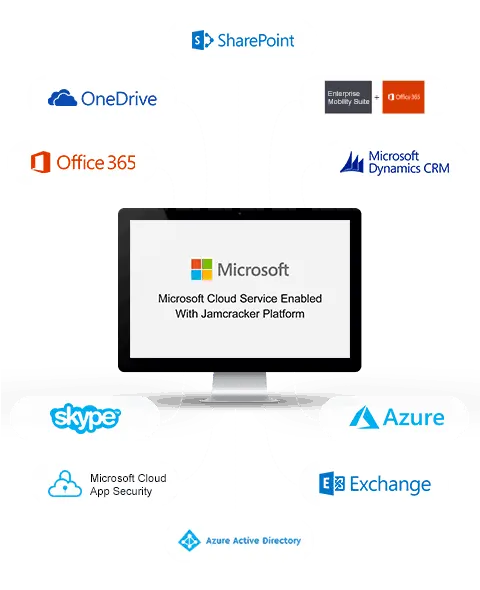
Accelerate go-to-market strategy with an end-to-end cloud services broker and management solution. Why leading Direct and Indirect Microsoft CSP Partners choose Jamcracker for their business?