Enterprise cloud computing has transformed IT. Cloud computing decreases time-to-market, improves agility by allowing businesses to adapt quickly to changing market demands, and, ultimately, drives down costs.
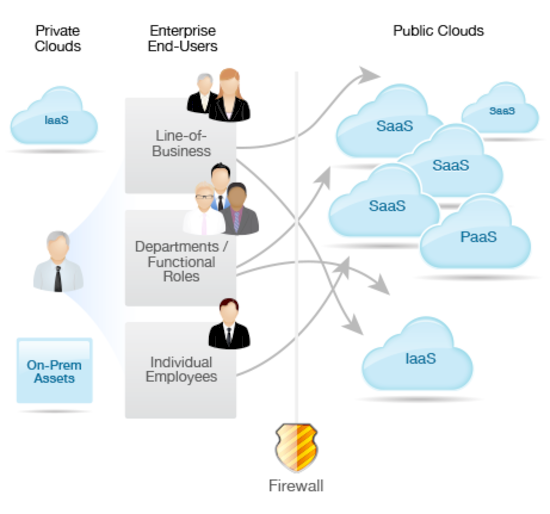
The ease of deploying and scaling cloud services, along with their low cost of acquisition, has resulted in increasingly decentralized IT, or what is referred to as “shadow IT.” This helps organizations become more agile, but it also increases security threats due to absence of governance, uniform information security, and adherence to regulatory compliance requirements.
Central IT has since reasserted itself in its domain, acting as a cloud broker to the enterprise. Moreover, citing security and budget issues, most organizations now require their departments to go through central IT to gain access to cloud services. Given the inconvenience of managing services, many departments are happy to cede control and service-management responsibilities to IT.
Ad-hoc adoption of clouds by departments, lines of business, and individual employees is putting pressure on enterprise IT administrators and CIOs.
According to Gartner, 42% of IT-related spending is now funded outside the standard IT budget. For many CIOs/CISOs, this raises significant concerns regarding governance:
- Compliance: IT's visibility as to the location of corporate data and its ability to control access policies
- Auditability: policy enforcement traceability and optimization of license management
- Accountability: the ability to track and control cloud spend by implementing enterprise-wide licensing and departmental chargeback capabilities across all external and internal services used by the organization
- Supportability: enabling provisioning, administration and support for external services that are procured directly from external providers without IT involvement
- Accessibility: implementing roles-based access control and enabling automated provisioning via services catalogs
- Security: enforcing corporate password policies and limiting the proliferation of passwords by employees (and ex-employees) for the use of public cloud services purchased by departmental users
The reality is that IT cannot govern what it cannot see, and therefore does not have the ability to control access and usage. But how should IT manage a changing environment such as this? In other words, how can companies provide for comprehensive cloud governance, while taking advantage of cloud business benefits of cost savings, agility, and productivity?
[This is part of the Cloud Governance and Management Series. Check out the other posts!]